The HIPAA Wall of Shame is a highly visible reminder that data breaches involving protected health information are real, and can have serious consequences for all involved. You can learn more about the Wall of Shame, what it includes, detailed examples of past incidents, and how to protect your data from being exposed by reading on.
In this Article …
- What is the HIPAA Wall of Shame?
- Why does the HIPAA Wall of Shame exist?
- What is protected health information?
- What information is included on the HIPAA Wall of Shame?
- Detailed examples of HIPAA data breaches that have occurred
- Tips and best practices for protecting data and maintaining compliance with HIPAA laws
What is the HIPAA Wall of Shame?
The HIPAA Wall of Shame refers to a website managed by the Department of Health and Human Services (HHS), Office for Civil Rights (OCR) that lists companies and individuals who have had data breaches affecting 500 or more individuals. Specifically, these breaches are a violation of the Health Insurance Portability and Accountability Act (HIPAA), the federal law that covers the privacy of protected health information (PHI).
The moniker “HIPAA Wall of Shame” is an informal and unofficial name often used within official ranks and the healthcare industry at large due to the site’s public display of those who have found themselves listed there.
It’s presumed that the majority of parties listed on this site likely had gaps in their compliance measures that put them at risk for a breach, and that eventually caught up with them. But, sadly, sometimes the specific circumstance of the incident may have resulted in a breach through little fault of their own, and the covered entity’s reputation is unsparingly marred. Officially, the website is called the Breach Notification Portal.
Those covered entities that are displayed on this site are listed as either Under Investigation, where the trailing twenty-four months of new violators are posted, or in the Archive portion of the site where older breaches and all their details will remain as a permanent record. As of the writing of this article, the total number of cases listed since its 2009 inception are …
- Under Investigation (trailing 24 months) – 876 cases
- Archive – 4,311 cases
- Data breach total since inception – 5,187 cases
Why does the HIPAA Wall of Shame exist?
Language in the HITECH Act of 2009 required HHS to create what has since become known as the HIPAA Wall of Shame.
“13402(e)(4): POSTING ON HHS PUBLIC WEBSITE.—The Secretary shall make available to the public on the Internet website of the Department of Health and Human Services a list that identifies each covered entity involved in a breach described in subsection (a) in which the unsecured protected health information of more than 500 individuals is acquired or disclosed.”
This public posting acts both as a disclosure to the public about breaches reported, and also to remind people not to take their data security for granted. Providing this information in one place serves as an important reminder that data breaches can occur at any time if proper measures aren’t taken.
What is protected health information?
Protected health information (PHI) is any data that relates to a person’s physical or mental health, their payment for healthcare services, and any other identifiable information related to the provision of healthcare. PHI includes personal identifiers such as name, address, age, Social Security number, email address, photographs, voice recordings, genetic data, and more. In addition to being known as Protected Health Information, or as the acronym “PHI”, it is also commonly referred to as Electronic Protected Health Information, or “ePHI” when the data is strictly in digital form, as in an electronic health record (EHR).
What information is included on the HIPAA Wall of Shame?
In adherence with the HITECH Act, the breach notification portal provides considerable insight into HIPAA security breaches to date.
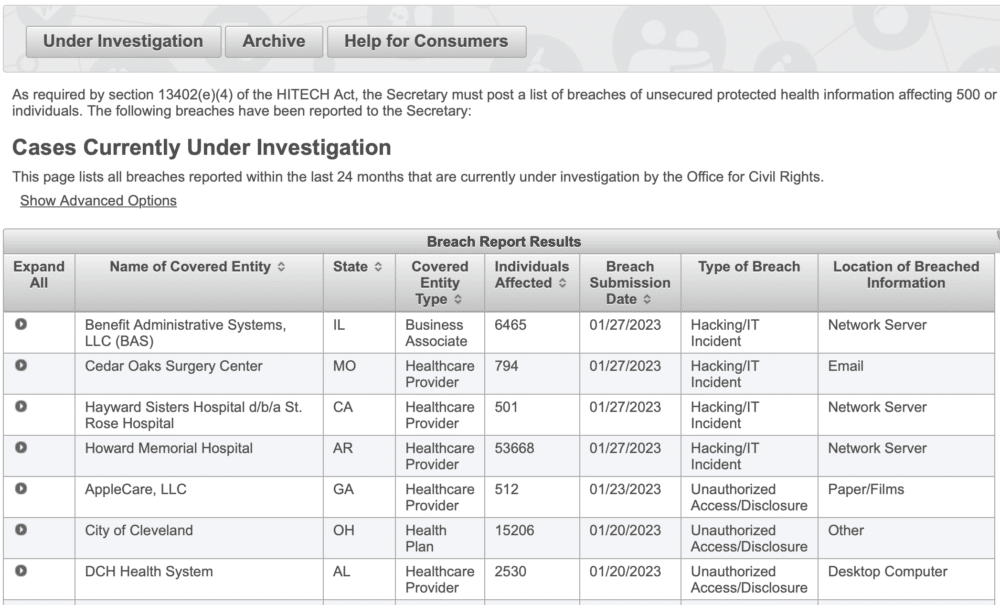
The following table provides details about the specific breach information that’s available for each record, and reflected on the image above.
| Name of Covered Entity | The legal name of the healthcare organization or individual where the breach occurred. |
| State | The state that the covered entity is located in. |
| Covered Entity Type | Health Plan, Healthcare Clearing House, Healthcare Provider, (Business Associate may be listed here if one was involved in the breach) |
| Individuals Affected | The total number of individuals whose protected data was involved in the reported breach. |
| Breach Submission Date | Formal reporting date of the breach to the Secretary of HHS. |
| Type of Breach | Hacking/IT Incident, Improper Disposal, Loss, Theft, Unauthorized Access/Disclosure, Unknown, or Other. |
| Location of Breached Information | Desktop Computer, Electronic Medical Record, Email, Laptop, Network Server, Other Portable Electronic Device, Paper/Films, or Other. |
| Expand All | Those under current investigation do not yet list additional except whether or not a Business Associate was involved in the breach. However, those that are now archived have additional descriptive information about the nature of the breaches reported. |
In the upper left of the screen, there is a link to advanced search options. Clicking on it reveals an expanded menu that allows for the filtering of all fields in the table of records. This allows for the ability to quickly find a specific record or to easily look at groups of records that share similar traits.
Detailed examples of HIPAA data breaches that have occurred
To provide you with a sampling of actual submissions to the HHS/OCR breach portal, what follows are three actual breach cases listed on “the wall”. The descriptions reflect the actual text from the public record.
Included are one Health Plan, one Business Associate, and one Healthcare Provider, and were the result of a hacking/ IT incident, a theft, and of an unauthorized access.
Anthem Inc.
|
“On March 13, 2015, Anthem filed a breach report with the HHS Office for Civil Rights detailing that, on January 29, 2015, they discovered cyber-attackers had gained access to their IT system via an undetected continuous and targeted cyberattack for the apparent purpose of extracting data, otherwise known as an advanced persistent threat attack. After filing their breach report, Anthem discovered cyber-attackers had infiltrated their system through spear phishing emails sent to an Anthem subsidiary after at least one employee responded to the malicious email and opened the door to further attacks. OCR’s investigation revealed that between December 2, 2014, and January 27, 2015, the cyber-attackers stole the ePHI of almost 79 million individuals, including names, social security numbers, medical identification numbers, addresses, dates of birth, email addresses, and employment information.
“In addition to the impermissible disclosure of ePHI, OCR’s investigation revealed that Anthem failed to conduct an enterprise-wide risk analysis, had insufficient procedures to regularly review information system activity, failed to identify and respond to suspected or known security incidents, and failed to implement adequate minimum access controls to prevent the cyber-attackers from accessing sensitive ePHI, beginning as early as February 18, 2014. “In addition to the $16 million settlement, Anthem will undertake a robust corrective action plan to comply with the HIPAA Rules. The resolution agreement and corrective action plan may be found on the OCR website at http://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/agreements/anthem/index.html.” |
GRM Information Management Services
|
“Unencrypted clinical system backup tapes that contained the electronic protected health information (ePHI) of 1,700,000 individuals were stolen from the unlocked vehicle of an employee of the covered entity’s (CE) business associate (BA). The ePHI included names, medical record numbers, social security numbers, addresses, telephone numbers, health plan numbers, dates of birth, dates of admission, dates of treatment, dates of discharge, dates of death, mother’s name, next of kin, clinical information related to diagnosis, treatment, prognosis, laboratory tests and results, and medications. Upon discovery of the breach, the CE filed a police report to recover the stolen items and provided breach notification to HHS, the media, and affected individuals. As a result of OCR’s investigation, the CE terminated its BA agreement and installed encryption software on backup media. The breach incident involved a BA and occurred prior to the September 23, 2013, compliance date. OCR verified that the CE had a proper BA agreement in place that restricted the BA’s use and disclosure of PHI and required the BA to safeguard all PHI.” |
Commonwealth Health Corporation
|
“Commonwealth Health Corporation, the covered entity (CE), discovered that, in August 2014 and February 2015, an employee impermissibly disclosed the protected health information (PHI) of 117,425 patients to a vendor. The types of PHI included billing information, patients’ names, addresses, social security numbers, health insurance information, diagnoses, procedure codes and charges for medical services. The CE sent timely breach notification to HHS. Pursuant to a law enforcement delay, the CE did not send individual notification, media notification or post notification on its website until March 21, 2017, and March 24, 2017. In response to the breach, the CE sanctioned the party responsible for the breach, retrained staff, adopted new policies and procedures, revised existing policies and procedures, and formalized existing procedures that were not previously in writing. OCR also provided technical assistance regarding safeguards for reactivating users in its IT system. OCR obtained assurances that the CE implemented the corrective actions listed above.” |
Tips and best practices for protecting data and maintaining compliance with HIPAA laws
When it comes to HIPAA compliance, the old adage, “An ounce of prevention is worth a pound of cure.” couldn’t be more applicable than it is here. This is because there are so many things that healthcare organizations can do to mitigate the potential of a HIPAA breach in the first place. And if one was to occur, there are equally so many things that can be done correctly to minimize the damage.
Consider the following …
- Appoint a HIPAA compliance officer to oversee privacy and security issues.
- Organize an effective Compliance Committee
- Adopt policies and procedures for complying with HIPAA rules.
- Develop and implement training for employees on HIPAA compliance.
- Deploy physical, technical, and administrative safeguards.
- Conduct Periodic HIPAA Risk Assessments.
- Respond quickly when offenses are discovered and implement necessary corrective actions.
- Get proper agreements in place with business associates and with all necessary third parties.
Need some help? Let us know. Some of this can be a bit complicated and intimidating. However, together we can certainly get you on the right path going forward pretty quickly.
Consider it to be an ounce of prevention.

